Mobile electronic fenceIs a collection of user mobile phone identification code(Equipment of IMEI and IMSI. By deploying a certain number of front-end acquisition devices at the corresponding points, the device obtains the mobile phone identification codes of past personnel and sends them to the background for storage and analysis. In the case that there is no suspected target after the incident, through the analysis of a considerable number of equipment data, multi-point series into lines to depict the trajectory of user activities, so as to fully grasp the importance of user access.
U automatic acquisition and analysis
When the user enters the device coverage area, the user's mobile phone logo code(IMSI/IMEI) Automatic collection and analysis;
U does not affect communication
When the user is in the state of call, the call will not be interrupted.
U information acquisition is fast
The acquisition speed is fast and won't attract users'attention.
U automatically identifies time, place and other related information
The time and place of acquisition can be automatically identified after acquisition of signals by the equipment, and the correlation degree analysis can be carried out more quickly.
U Multiple transmission modes
Supporting multiple means of data transmission, reliable data transmission, wired network, wireless, etc.WiFiVarious transmission modes;
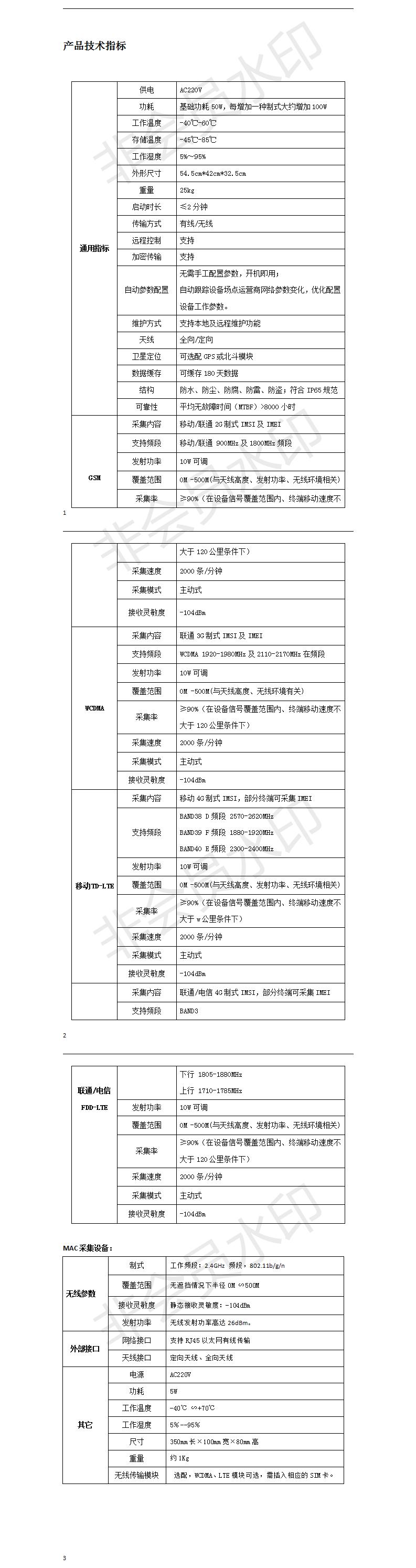
u Hot-spot equipment acquisition system is divided intoGSM, WCDMA, TDD-LTE, FDD-LTE system, the frequency band of acquisition is complete;
u Receiving sensitivity <-104dBm;
u The acquisition content is mobile terminal signatureIMSI;
u The coverage distance is0-500m (depending on wireless environment and transmission power);
u Acquisition rateMore than 85% (under the condition of equipment signal coverage and terminal moving speed less than 120 km);
u Support docking with other related systemsData fusion;
The transmitting power of U equipment can be continuously adjusted and closed.
u The acquisition speed is per minute.More than 1200;
u Release time of acquisition terminal is less than10 seconds;
u Front-end devices support data local storage and cache satisfaction180 days demand, more than 1 million pieces of information, storage and expansion capacity. When the storage is full, the earlier data is automatically deleted.
U supports both wireless and wired transmission modes.
u SupportMore than three transmit antennas can be set according to the environment.
U satisfies the function of waterproof, dust-proof, anticorrosion, lightning-proof and theft-proof.
u System recovery time is less than2 minutes;
U has the function of remotely configuring and restarting the front-end equipment system.
u Adapt to a variety ofStandard system
It can meet the requirements of mobile, Unicom and telecom full-scale acquisition.
U has good concealment
The appearance of the equipment is the same as that of the ordinary chassis, which makes it difficult for people in public places to distinguish and expose.
U Protects User Privacy
Only the user's mobile phone identification number is collected, and personal information such as name, address and so on is not involved.
U high yield, stable operation, high accuracy of data acquisition
High security of u transmission
Location record of activities, better help to crack, capture and other operations.